Introduction Cyber attacks are evolving faster than most organisations can defend against. For many years, security teams relied on signature-based antivirus, known threat databases, and predefined detection rules to stop malicious software. However, a new generation of threats has emerged — AI-enabled malware — and it changes the game entirely. Unlike traditional malware, which is...
ICCSO: Championing Collective Resilience and Best Practice Sharing in Cybersecurity
In today’s dynamic cyber threat landscape, collaboration has become essential for organizations seeking to protect themselves, their stakeholders, and the communities they serve. The International Consortium for Cyber Security Operations (ICCSO), a nonprofit dedicated to advancing cybersecurity resilience, brings together nonprofits, businesses, academic institutions, and professionals to build a stronger, safer digital future for all....
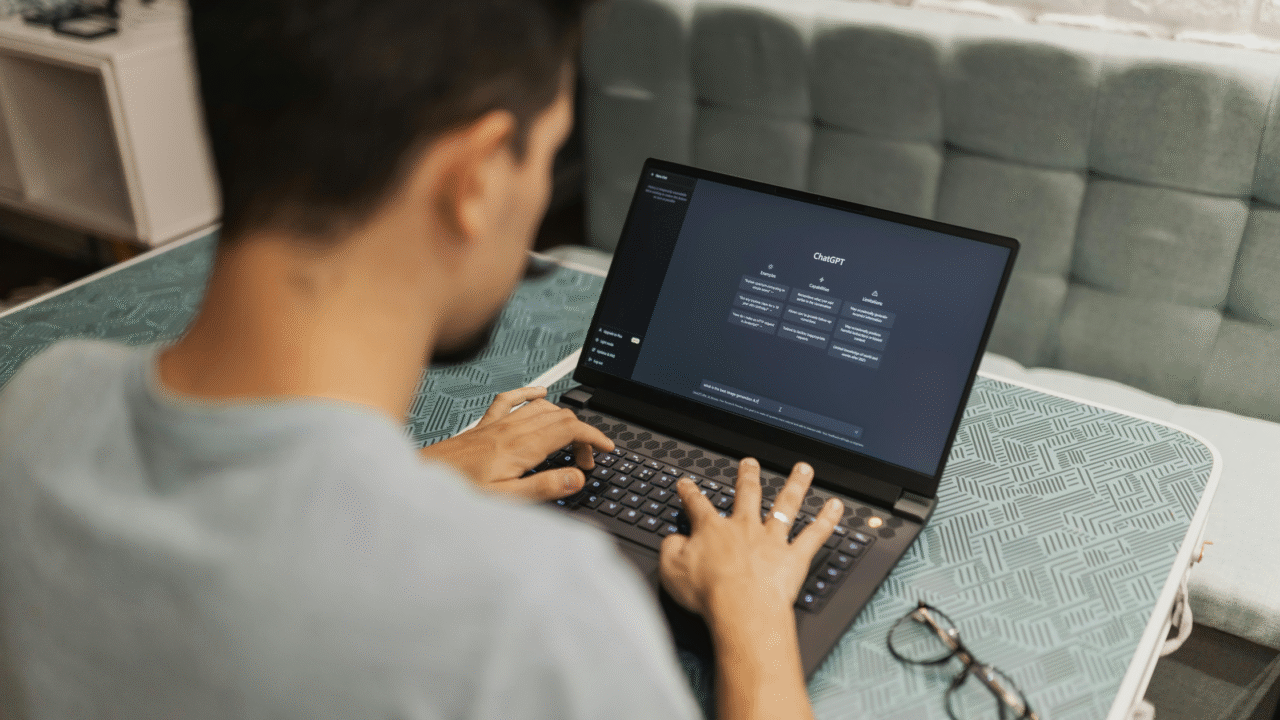
New Exploit in ChatGPT Atlas Browser Exposes Emerging AI Security Vulnerabilities
Overview A newly uncovered vulnerability in OpenAI’s ChatGPT Atlas Browser Mode has raised significant concern within the global cybersecurity community. Security researchers discovered that attackers can exploit this feature to inject persistent hidden commands directly into the AI’s operational memory. This exploit, if leveraged, allows threat actors to execute unauthorised actions, retrieve sensitive data, or...
ICCSO Joins the UK Government’s CyberFirst® Programme
The International Consortium for Cyber Security Operations C.I.C. (ICCSO) is delighted to announce that it has joined the UK Government’s CyberFirst® Programme as an official Member. This new association reflects ICCSO’s ongoing commitment to building a strong and resilient cyber security ecosystem in the United Kingdom and to investing in the next generation of cyber...
Large Language Models and Cybersecurity: Opportunities, Risks, and the Road Ahead
The rapid rise of Artificial Intelligence (AI) and Large Language Models (LLMs) is reshaping industries across the world. From healthcare and education to financial services, these models are enabling unprecedented levels of automation, creativity, and efficiency. In the domain of cybersecurity, however, the impact of LLMs is particularly profound. Cybersecurity professionals are facing a constantly...
Safeguarding Operational Technology (OT): Latest Use Cases, Risks & ICCSO Recommendations
Operational Technology (OT) — the hardware and software systems that monitor and control industrial processes, manufacturing plants, utilities, and critical infrastructure — is under mounting pressure. With digital transformation accelerating and IT/OT convergence becoming the norm, attackers now have new entry points to exploit legacy vulnerabilities and poorly segmented environments. This article explores why OT...
Psychology and Cybersecurity: Understanding the Human Factor in Digital Defense
Introduction In the modern digital era, organizations invest millions in firewalls, encryption, intrusion detection systems, and artificial intelligence for cyber defense. Yet, time and again, cybercriminals bypass these sophisticated barriers not by breaking code, but by breaking people. The reality is that the human mind is the most vulnerable endpoint. At the International Consortium for...
AI Agents in Cybersecurity: The Double-Edged Sword
Artificial Intelligence (AI) has moved from hype to reality in the field of cybersecurity. With threats evolving in complexity and scale, organizations are under constant pressure to strengthen their defenses while keeping costs and human fatigue in check. One of the most significant developments in this space is the rise of AI agents — autonomous,...
Why Supply Chain Attacks Are the New Frontier of Cyber Warfare
Introduction: A Shifting Battlefield The nature of cyber conflict is evolving at a pace few could have predicted. Traditional defenses once focused on protecting corporate networks and endpoints, but today’s adversaries are no longer just targeting the organization itself. They are going after the weakest link—the supply chain. Every enterprise is now part of a...
Jaguar Land Rover Halts Operations Following Major Cyberattack
London, UK — Jaguar Land Rover (JLR), the UK’s largest car manufacturer, has temporarily shut down several operations after a significant cyberattack disrupted its digital infrastructure earlier this week, the company confirmed Tuesday. The breach, which reportedly targeted the automaker’s IT systems over the weekend, has affected both production and internal communications, forcing a partial...